Choose a different version or distribution
Introduction
Before we begin talking about how to install Fail2ban, let's briefly understand – What is Fail2ban?
Fail2ban is a powerful security tool that safeguards your computer systems from malicious attacks. It automatically detects and blocks suspicious activity by monitoring log files for repeated login failures or unauthorized access attempts.
By swiftly banning these offenders, Fail2ban enhances your system's defense, reducing the risk of unauthorized intrusion. With its straightforward setup and customizable settings, Fail2ban is an essential solution for enhancing the security of your online infrastructure.
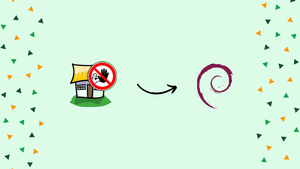
In this tutorial, you will install and configure Fail2ban on Debian 10.
Advantages of Fail2ban
- Enhanced Security: Fail2ban swiftly identifies and blocks suspicious activity, preventing unauthorized access to your systems.
- Automated Protection: It automatically monitors log files, saving time and effort by banning malicious actors without manual intervention.
- Customizable Settings: Fail2ban allows you to tailor its rules and actions to meet your specific security needs.
- Versatility: It can be applied to various services like SSH, FTP, and web servers, providing comprehensive protection for different applications.
- Easy Setup: Fail2ban offers a user-friendly interface, making it accessible even for those with limited technical expertise.
Install Fail2ban on Debian
The default Debian 10 repositories contain the Fail2ban package. Execute the command below as root or user with sudo privileges to install it:
sudo apt update
sudo apt install fail2ban
The Fail2ban service will launch immediately after completion. You can confirm it by checking the service status:
sudo systemctl status fail2ban
The result will appear as follows:
Output
● fail2ban.service - Fail2Ban Service
Loaded: loaded (/lib/systemd/system/fail2ban.service; enabled; vendor preset: enabled)
Active: active (running) since Wed 2021-03-10 18:57:32 UTC; 47s ago
...
All done. Now you have Fail2Ban operating on your Debian server.
Fail2ban Configuration
There are two configuration files included with the Fail2ban installation by default: /etc/fail2ban/jail.conf and /etc/fail2ban/jail.d/defaults-debian.conf. These files should not be modified since they may be overwritten when the package is updated.
The configuration files are read by Fail2ban in the following order. The settings from each .local file take precedence over those from the .conf file:
/etc/fail2ban/jail.conf/etc/fail2ban/jail.d/*.conf/etc/fail2ban/jail.local/etc/fail2ban/jail.d/*.local
The simplest approach to set up Fail2ban is to copy jail.conf to jail.local and make changes to the .local file. Users with more experience can create a .local configuration file from start. Only the settings you want to override from the corresponding .conf file must be included in the .local file.
Make a .local configuration file by copying the default jail.conf file:
sudo cp /etc/fail2ban/jail.{conf,local}
Opening the jail.local file in your text editor allows you to start establishing the Fail2ban server:
sudo nano /etc/fail2ban/jail.local
The file provides comments that explain what each configuration option accomplishes. We'll adjust the fundamental settings in this example.
Whitelist IP Addresses
You can add hosts, IP addresses, or IP ranges to the ignoreip directive to prevent them from being blocked. Your local PC's IP address and the addresses of all additional devices you want to whitelist should be added here.
Uncomment the line beginning with ignoreip and enter your IP addresses separated by space:
ignoreip = 127.0.0.1/8 ::1 123.123.123.123 192.168.1.0/24
Ban Settings
The bantime, findtime, and maxretry options set the ban period and the ban requirements.
The timeframe of the IP ban is known as the bantime. When no suffix is supplied, seconds are used by default. The bantime value is initially set to 10 minutes by default. Most users favor setting a longer ban duration. Adjust the value to your preference:
bantime = 1d
Use a negative value to block the IP address permanently.
The amount of time between failures before a ban is set is known as findtime. For instance, if Fail2ban is configured to ban an IP address after five attempts ( maxretry, see below), those attempts must fail within the findtime period.
findtime = 10m
The number of failures before an IP address is blocked is defined as maxretry. The default value is five, which should be sufficient for most users.
maxretry = 5
Email Notifications
When an IP has been blacklisted, Fail2ban can send email alerts. You must have an SMTP installed on your server in order to receive emails. You must also modify the default action, which just restricts the IP to %(action_mw)s, as seen below:
action = %(action_mw)s
In addition to blocking the offending IP, %(action_mw)s sends an email with a whois report. Set the action t0 %(action_mwl)s to include the pertinent logs in the email.
You can also modify the email addresses used for sending and receiving messages:
destemail = [email protected]
sender = [email protected]
Fail2ban Jails
Fail2ban employs the concept of jails. A jail describes a service that comprises filters and actions. The number of log entries that fit the search pattern is counted, and when predetermined criteria are fulfilled, the relevant actions are carried out.
Fail2ban comes with a variety of jails for various types of services. Furthermore, you can design your own jail setups. By default, only the ssh jail is enabled.
You must include enabled = true after the jail title in order to enable a jail. The postfix jail can be enabled using the example below:
[postfix]
enabled = true
port = smtp,ssmtp
filter = postfix
logpath = /var/log/mail.log
The options we covered in the preceding section can be modified for each jail. Here's an example:
[sshd]
enabled = true
maxretry = 3
findtime = 1d
bantime = 4w
ignoreip = 127.0.0.1/8 11.22.33.44
The filters are stored in a file with the same name as the jail in the /etc/fail2ban/filter.d directory. You can fine-tune the filters if you have a custom configuration and experience with regular expressions.
The Fail2ban service must be restarted after each modification to the configuration file in order for the changes to take effect:
sudo systemctl restart fail2ban
Fail2ban Client
You can communicate with the Fail2ban service using the command-line tool fail2ban-client that comes with Fail2ban.
Use the -h option when executing the command to see all available options:
fail2ban-client -h
With the help of this tool, you may ban or unban IP addresses, modify the settings, restart the service, and more. Here are a few examples:
- Retrieve the server's current status:
sudo fail2ban-client status
- Verify the jail status:
sudo fail2ban-client status sshd
- Unban an IP:
sudo fail2ban-client set sshd unbanip 11.22.33.44
- Ban an IP:
sudo fail2ban-client set sshd banip 11.22.33.44
FAQs to Install Fail2ban on Debian 10
What log files does Fail2ban monitor?
Fail2ban monitors various log files, including those for SSH, FTP, and web servers, to identify and block malicious activity.
Can I customize Fail2ban's settings?
Yes, Fail2ban allows you to customize its rules and actions to suit your specific security requirements.
Does Fail2ban automatically ban offenders?
Yes, Fail2ban automatically bans IP addresses that repeatedly fail authentication or engage in suspicious activity.
How does Fail2ban help enhance security?
Fail2ban strengthens security by swiftly blocking malicious actors, reducing the risk of unauthorized access to your system.
Are there any other system requirements for Fail2ban on Debian 10?
Fail2ban typically works well on Debian 10 without additional system requirements.
Can I uninstall Fail2ban if needed?
Yes, you can uninstall Fail2ban from Debian 10 by running the command "sudo apt-get remove fail2ban" in the terminal.
Does Fail2ban provide real-time alerts?
Yes, Fail2ban can be configured to send real-time alerts via email or other methods when it detects suspicious activity.
Conclusion
In this tutorial, you installed and configured Fail2ban on Debian 10. Visit the Fail2ban documentation for more details on this subject.
If you have any queries, please leave a comment below and we’ll be happy to respond to them.