Choose a different version or distribution
Introduction
Before we begin talking about how to install apache web server on centos 8, let's briefly understand – What is Apache Web Server ?
Apache HTTP Server, commonly referred to as Apache, is a widely-used open-source web server software. Installing Apache Web Server on CentOS 8 allows you to host and serve web content efficiently.
This tutorial will guide you through the process of installing Apache Web Server on CentOS 8.
Advantages of Installing Apache Web Server on CentOS 8
- Open-source and Reliable: Apache Web Server is widely used, supported by a strong community, and has a proven track record of reliability and security.
- Extensible and Customizable: Apache offers a range of modules that allow you to extend the functionality of the web server and customize it based on specific requirements.
- Performance and Scalability: Apache Web Server is highly efficient and scales well, allowing you to handle high traffic loads and efficiently serve web content.
- Integration with other Technologies: Apache Web Server seamlessly integrates with PHP, Python, Perl, and other scripting languages, enabling dynamic web content generation.
- Robust Security Features: Apache Web Server provides various security features like SSL/TLS encryption, access control, authentication, and logging to help protect websites and web applications.
Prerequisites
To finish this tutorial, you will require the following:
- A non-root user with sudo privileges set up on your server, created by following the CentOS 8 initial server setup guidelines.
- By following Step 4 of the Initial Server Setup with CentOS 8 (recommended) in the above instructions, make sure that a fundamental firewall is configured.
Step 1 — Installing Apache
Apache may be installed using the dnf package manager because it is part of CentOS's default software repository.
Install the Apache package as the non-root sudo user specified in the prerequisites:
sudo dnf install httpd
dnf will install Apache and all necessary components when you confirm the installation.
You can serve HTTP requests on your server by installing firewalld by completing Step 4 of the Initial Server Setup with CentOS 8 instruction, which is listed in the prerequisites section.
You should additionally open up port 443 by turning on the https service if you intend to configure Apache to serve content over HTTPS:
sudo firewall-cmd --permanent --add-service=https
To apply the updated rules, restart the firewall:
sudo firewall-cmd --reload
You can start the service and inspect the web server after the firewall has finished reloading.
Step 2 — Checking your Web Server
Once the installation is complete on CentOS, Apache does not start automatically; therefore, you must manually start the Apache process:
sudo systemctl start httpd
Execute the following command to check that the service is active:
Output
● httpd.service - The Apache HTTP Server
Loaded: loaded (/usr/lib/systemd/system/httpd.service; disabled; vendor preset: disa>
Active: active (running) since Thu 2020-04-23 22:25:33 UTC; 11s ago
Docs: man:httpd.service(8)
Main PID: 14219 (httpd)
Status: "Running, listening on: port 80"
Tasks: 213 (limit: 5059)
Memory: 24.9M
CGroup: /system.slice/httpd.service
├─14219 /usr/sbin/httpd -DFOREGROUND
├─14220 /usr/sbin/httpd -DFOREGROUND
├─14221 /usr/sbin/httpd -DFOREGROUND
├─14222 /usr/sbin/httpd -DFOREGROUND
└─14223 /usr/sbin/httpd -DFOREGROUND
This output shows that the service has successfully started. The best way to test this, though, is to request a page from Apache.
You can view the default Apache landing page using your IP address to verify the programme is operating correctly. There are several ways to obtain your server's IP address from the command line if you are unsure of it.
Returning to the command prompt by typing q, type the following:
hostname -I
You will receive back a list of IP addresses separated by spaces because this command will reveal all the host's network addresses. You can check to see if they all work on your web browser.
As an alternative, you can use curl to ask icanhazip.com for your IP, which will provide your public IPv4 address as read from another internet location:
curl -4 icanhazip.com
Once you are aware of your server's IP address, enter it into your browser's address bar as shown below:
http://your_server_ip
The default CentOS 8 Apache web page will appear:
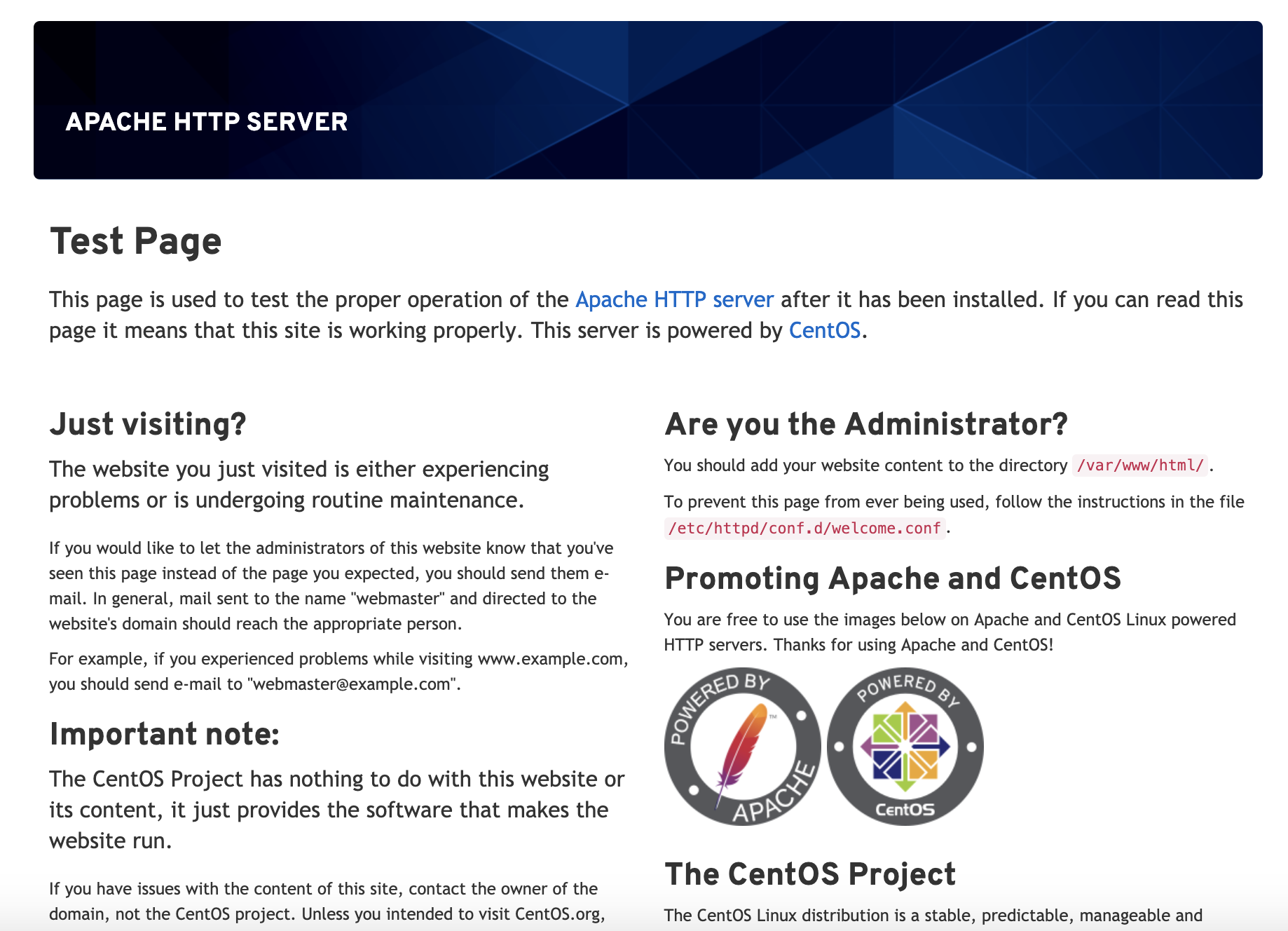
This page shows that Apache is operating properly. It also includes some basic information on where important Apache files and directories are located.
Step 3 — Managing the Apache Process
You can use various systemctl commands to manage the service now that it has been deployed and is operational.
Type the following to terminate your web server:
sudo systemctl stop httpd
To restart the web server once it has been shut down, enter:
sudo systemctl start httpd
To stop and then restart the service, enter:
sudo systemctl restart httpd
Most of the time, Apache can reload without losing connections if you are only making configuration changes. Use this command to accomplish this:
sudo systemctl reload httpd
Apache is by default configured to start immediately when the server boots. Disable this behaviour if it is not what you want by typing:
sudo systemctl disable httpd
Enter the following command to make the service bootable once more:
sudo systemctl enable httpd
When the server restarts, Apache will now start by itself.
Your server may host one website thanks to Apache's default configuration. You must set up virtual hosts on your Apache web server if you intend to host numerous domains on the same machine.
Step 4 — Configuring Virtual Hosts (Recommended)
When utilizing the Apache web server, you can use virtual hosts (similar to server blocks in Nginx) to encapsulate configuration data and host more than one domain from a single server. You will create the domain example.com in this stage, but you should use your own domain name instead. Please read our Networking Documentation if you are setting up a domain name with DigitalOcean.
One virtual host is enabled by default for Apache on CentOS 8, and it is set up to serve files from the /var/www/html directory. Even if this works for one site, hosting numerous sites could make it difficult. Instead of changing /var/www/html, you should build a directory structure within /var/www for the example.com site. If a client request doesn't match any other sites, /var/www/html will still be delivered by default.
Create the html directory for example.com as follows, using the -p command to create any necessary parent directories:
sudo mkdir -p /var/www/example.com/html
Create a new directory to store the site's log files:
sudo mkdir -p /var/www/example.com/log
Next, use the $USER environmental variable to determine who is in charge of the html directory:
sudo chown -R $USER:$USER /var/www/example.com/html
Ensure that the default permissions are configured for your web root:
sudo chmod -R 755 /var/www
Making a sample index.html page is next. Use vi or your favourite editor to create the following page:
sudo vi /var/www/example.com/html/index.html
To enter INSERT mode, press i, then paste the ensuing example HTML into the file:
<html>
<head>
<title>Welcome to Example.com!</title>
</head>
<body>
<h1>Success! The example.com virtual host is working!</h1>
</body>
</html>
Press ESC, enter :wq, and press Enter to save and close the document.
You are almost ready to generate the virtual host files now that your site directory and sample index file are established. Virtual host files define the setup of your individual sites and instruct the Apache web server on how to respond to specific domain requests.
To store your virtual hosts, you must first establish a directory called sites-available. The sites-enabled directory, which informs Apache that a virtual host is prepared to serve visitors, will also be created by you. We will store symbolic links to the virtual hosts we intend to publish in the sites-enabled directory. Use the command below to create both directories:
sudo mkdir /etc/httpd/sites-available /etc/httpd/sites-enabled
The next step is to direct Apache to search the sites-enabled directory for virtual hosts. To do this, add a line declaring an optional location for additional configuration files to Apache's main configuration file using vi or your preferred text editor:
sudo vi /etc/httpd/conf/httpd.conf
When you want to go to the end of the file, type capital G. Then, press i to enter INSERT mode, and add the next line at the end of the document:
...
# Supplemental configuration
#
# Load config files in the "/etc/httpd/conf.d" directory, if any.
IncludeOptional conf.d/*.conf
IncludeOptional sites-enabled/*.conf
Once you've finished adding that line, save the document and exit. You will make your virtual host file after setting up your virtual host folders.
Make a new file first in the sites-available directory:
sudo vi /etc/httpd/sites-available/example.com.conf
The following configuration block should be included, with your domain name substituted, for example.com in the code:
<VirtualHost *:80>
ServerName www.example.com
ServerAlias example.com
DocumentRoot /var/www/example.com/html
ErrorLog /var/www/example.com/log/error.log
CustomLog /var/www/example.com/log/requests.log combined
</VirtualHost>
This will instruct Apache where to look for the root directly, which contains the web files that are available to the public. Additionally, it instructs Apache where to put the request and error logs for this specific website.
When you're done, save and exit the file.
The virtual host files must now be enabled so that Apache knows to offer them to visitors after being built. To accomplish this, make a symbolic link in the sites-enabled directory for each virtual host:
sudo ln -s /etc/httpd/sites-available/example.com.conf /etc/httpd/sites-enabled/example.com.conf
Now that it has been set up, your virtual host is prepared to deliver content. Let's verify that SELinux has the appropriate policies in place for your virtual hosts before restarting the Apache service.
Step 5 — Adjusting SELinux Permissions for Virtual Hosts (Recommended)
A security component of the Linux kernel known as SELinux enhances security for Linux systems. SELinux is preconfigured in CentOS 8 to work with the default Apache configuration. If you try to start the Apache service after changing the default settings by creating a custom log directory in the virtual hosts configuration file, you will encounter an error. You must update the SELinux policies to permit Apache to write to the required files in order to fix this.
Since SELinux enables you to customize your security level, there are various ways to implement policies based on the requirements of your environment. The two ways to modify Apache policies will be covered in this step: globally and on a single directory. Changing the policies on directories makes them more secure and is therefore the recommended method.
Adjusting Apache Policies Universally
By using the httpd_unified Boolean, setting the Apache policy to universal will instruct SELinux to treat all Apache processes equally. Although this method is more practical, it won't provide you as much control as one that relies on file or directory policies.
To create a global Apache policy, issue the following command:
sudo setsebool -P httpd_unified 1
SELinux Boolean values can be changed with the setsebool command. The boot-time value will be updated by the -P flag, making the change durable across reboots. You have enabled httpd_unified with a value of 1 to instruct SELinux to treat all Apache processes as the same type.
Adjusting Apache Policies on a Directory
You will have greater control over your Apache policies if you individually configure the SELinux permissions for the /var/www/example.com/log directory, but it can also take more time. You must manually define the context type for any new log folders specified in your virtual host setups because this option does not virtually set policies.
Check the context type that SELinux assigned to the directory /var/www/example.com/log first:
sudo ls -dlZ /var/www/example.com/log/
The SELinux context of the directory is listed and printed by this command. The following output will be provided to you:
drwxr-xr-x. 2 root root unconfined_u:object_r:httpd_sys_content_t:s0 6 Apr 23 23:51 /var/www/example.com/log/
The Apache process can only read files produced in this directory, according to the SELinux directive httpd_sys_content_t, which is the current context. The /var/www/example.com/log directory's context type will be changed in this lesson to httpd_log_t. Apache will be able to create and append log files for web applications using this type:
sudo semanage fcontext -a -t httpd_log_t "/var/www/example.com/log(/.*)?"
Next, implement these modifications and make sure they last through reboots by using the restorecon command:
sudo restorecon -R -v /var/www/example.com/log
Any existing files will be updated to utilise the new context when this command is executed with the -R flag. The context modifications that the command made are printed using the -v flag. The changes will be verified by the output that you will see below:
Relabeled /var/www/example.com/log from unconfined_u:object_r:httpd_sys_content_t:s0 to unconfined_u:object_r:httpd_log_t:s0
To observe the changes, list the contexts once more:
sudo ls -dlZ /var/www/example.com/log/
The new context type is reflected in the output:
Output
drwxr-xr-x. 2 root root unconfined_u:object_r:httpd_log_t:s0 6 Apr 23 23:51 /var/www/example.com/log/
You can test your virtual host settings now that the httpd_log_t type is being used by the /var/www/example.com/log directory.
Step 6 — Testing the Virtual Host (Recommended)
With either approach, Apache will be able to write to the /var/www/example.com/log directory once the SELinux context has been updated. The Apache service can now be successfully restarted:
sudo systemctl restart httpd
To determine whether Apache produced the log files, list what is in the /var/www/example.com/log directory:
ls -lZ /var/www/example.com/log
When Apache successfully creates the error.log and requests.log files provided in the virtual host settings, you'll be informed:
Output
-rw-r--r--. 1 root root system_u:object_r:httpd_log_t:s0 0 Apr 24 00:06 error.log
-rw-r--r--. 1 root root system_u:object_r:httpd_log_t:s0 0 Apr 24 00:06 requests.log
Apache will now serve your domain name once your virtual host has been configured and SELinux permissions have been updated. Visit http://example.com to check this out. You should see something that resembles the following:
This verifies that your virtual host is properly set up and distributing content. To build new virtual hosts with SELinux rights for additional domains, repeat Steps 4 and 5.
FAQs on Installing Apache Web Server on CentOS 8
Is Apache Web Server compatible with CentOS 8?
Yes, Apache Web Server is fully compatible with CentOS 8.
How can I install Apache Web Server on CentOS 8 using the package manager?
To install Apache Web Server, open a terminal and run the command sudo dnf install httpd to install the Apache package using the dnf package manager.
What are the system requirements for installing Apache Web Server on CentOS 8?
To install Apache Web Server on CentOS 8, you need a CentOS 8 installation, terminal access with administrative privileges, and a stable internet connection.
What is the default configuration file for Apache Web Server on CentOS 8?
The main configuration file for Apache Web Server on CentOS 8 is /etc/httpd/conf/httpd.conf.
Is it possible to enable Apache Web Server to start automatically on system boot?
Yes, you can enable Apache Web Server to start automatically on system boot by running the command sudo systemctl enable httpd.
Where are the web files and documents stored for Apache Web Server on CentOS 8?
The default web files and documents are stored in the /var/www/html/ directory on CentOS 8.
Can I host multiple websites on a single Apache Web Server on CentOS 8?
Yes, Apache Web Server supports hosting multiple websites by configuring virtual hosts. Each website can have its own directory and configuration.
Conclusion
In this tutorial, you learned how to install and manage the Apache web server. Now that your web server is set up, you have a variety of options for the content types you can offer and the technologies you can utilize to give users a richer experience.
